Password hacks are becoming more common as people’s online accounts contain more sensitive personal data. Even big, trusted sites are suffering password breaches in the recently. And because most people reuse their passwords, it becomes more likely that a password hacked on one site can open accounts on other sites. Here are some tips to help prevent your data from being compromised.
Stay away from English-language passwords and short passwords
One of the biggest mistakes is using English words in your passwords. English words make hacking passwords far easier for a potential hacker. Given that there are only approximately 500,000 words in the English language, it takes only a few minutes (or less) for a computer to run a dictionary attack to guess your password. A more complex password would use random characters and numbers, but there are common misconceptions made here as well. Many mistakenly believe a password of 8 random characters is secure enough, but the calculating power of today’s computers can easily brute force all the possibilities in as little as 10 minutes. If you add digits to the mix, you increase the complexity enough for it to take 37 minutes. Adding symbols to the mix only increases the maximum time to crack to less than 19 hours.
Clearly, there needs to be more complexity to our password. Using a mix of upper case, lower case, numbers and symbols and increasing the password length to 12 characters will increase the complexity enough to require up to 1.74 thousand centuries for a brute force attack. But who wants to remember something that difficult. One solution is to use a passphrase. Passphrases increase the complexity but be careful to not use all dictionary words. For example, the passphrase “ilovemydogs” can be cracked in less than 11 hours, but “I luv my dogs!” would take over 3 million centuries to crack. Purposely misspelling words to replacing 1 or 2 letters with numbers will advert brute force attacks that may try to combine common dictionary works.
Have a favorite poem or song?
One of the easiest ways to create strong passwords is to use something that you’ve already committed to memory. Many articles have been published about using a “base password” to remember all other passwords by, and simply adding the name of a website to the end, such as for Amazon.com: passwordAMAZ. We wanted to take a different approach to implementing things you might have already committed to memory. For instance, let’s take a popular song like Twinkle Little Star:
“Twinkle twinkle little star, how I wonder what you are.”
Take the first two letters of each word, and you have: TWTWLISTHOIWIWHYOAR
Test your password
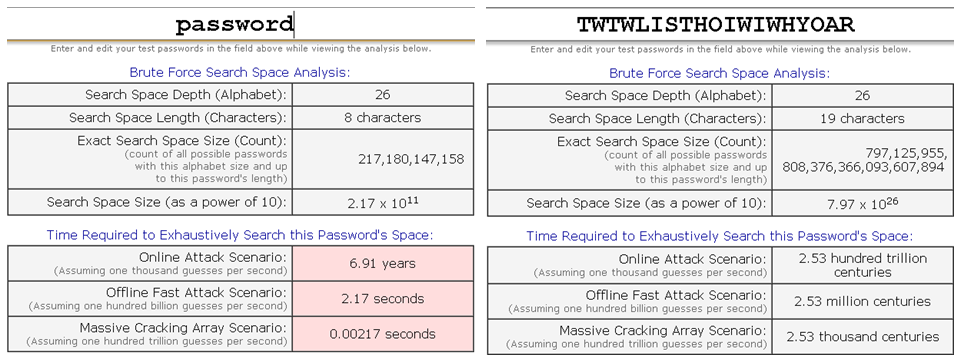
How strong is your password? One of the best ways to find out is to use GRC’s Brute Force Calculator at https://www.grc.com/haystack.htm. If you compare the word “password” to the Twinkle Little Star example from above:
Create fake security answers
Which street did you live on when you were ten? What is your mother’s maiden name? STOP. DO NOT SUPPLY THE CORRECT ANSWERS.
Think about it: if you give the correct answers to these questions, you’re giving companies and potential hackers even more extensive information about yourself. Plus anyone can find these answers on data broker websites for only a few dollars, so they’re hardly secure.
Giving the wrong answers to these questions, even answers that aren’t actual words can add another layer of protection. One example of how to use these questions: “Who was your first employer?” If your first job was working at McDonald’s, make your answer “The Clown”.